The Moment Healthcare IT Leaders Can No Longer Delay
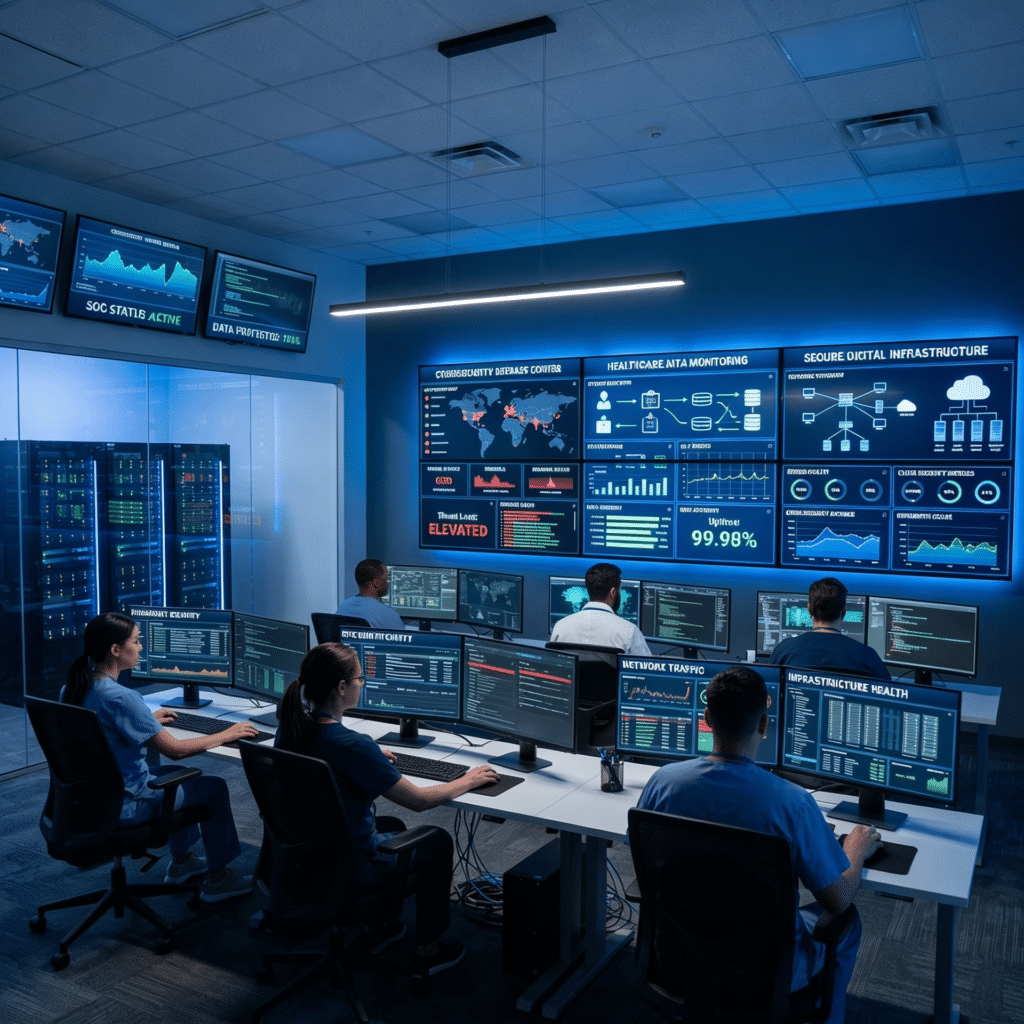
The conference room falls silent as the quarterly cybersecurity review begins. On the screen, the CIO of a regional healthcare network highlights a new reality facing the industry: the HIPAA Security Rule Changes 2026 are raising the standard for how healthcare organizations secure electronic protected health information (ePHI). Encryption is no longer treated as a recommendation. Multi-factor authentication (MFA) is becoming an expected baseline. Continuous monitoring, vulnerability testing, and documented recovery procedures are steadily moving from “best practices” into operational expectations regulators increasingly expect organizations to prove with evidence.
For many healthcare organizations, this shift creates immediate pressure. Their EHR environments are aging, legacy applications still depend on unsupported infrastructure, and several core systems were never designed to support modern identity controls or organization-wide encryption. At the same time, ransomware attacks against hospitals continue to increase in sophistication, frequency, and financial impact. As healthcare leaders prepare for the HIPAA Security Rule Changes 2026, these infrastructure weaknesses are becoming harder to ignore.
Across healthcare leadership teams, the same questions continue to surface. Where should modernization begin? How quickly can systems be secured without disrupting patient care? Which initiatives reduce risk immediately, and which projects require longer-term transformation under the HIPAA Security Rule Changes 2026?
The answer is not a rushed overhaul. It is a structured modernization roadmap focused on measurable progress, operational continuity, and compliance readiness.
At Vedhas Technology Solutions, modernization initiatives are approached through phased execution models that help healthcare organizations strengthen security while minimizing operational disruption. With experience in healthcare platforms, cloud modernization, enterprise application transformation, and compliance-aware infrastructure planning, Vedhas helps organizations modernize legacy environments in a controlled and scalable way.
This guide explains how healthcare organizations can respond to the HIPAA Security Rule Changes 2026 through a practical 90-day modernization strategy focused on encryption, MFA, infrastructure hardening, continuous testing, and governance readiness.
Why the HIPAA Security Rule Changes 2026 Matter?
The HIPAA Security Rule Changes 2026 represent one of the most significant shifts in healthcare cybersecurity expectations in years. Regulators are increasingly emphasizing that security safeguards must not only exist on paper but also operate consistently across the organization with measurable evidence supporting their effectiveness.
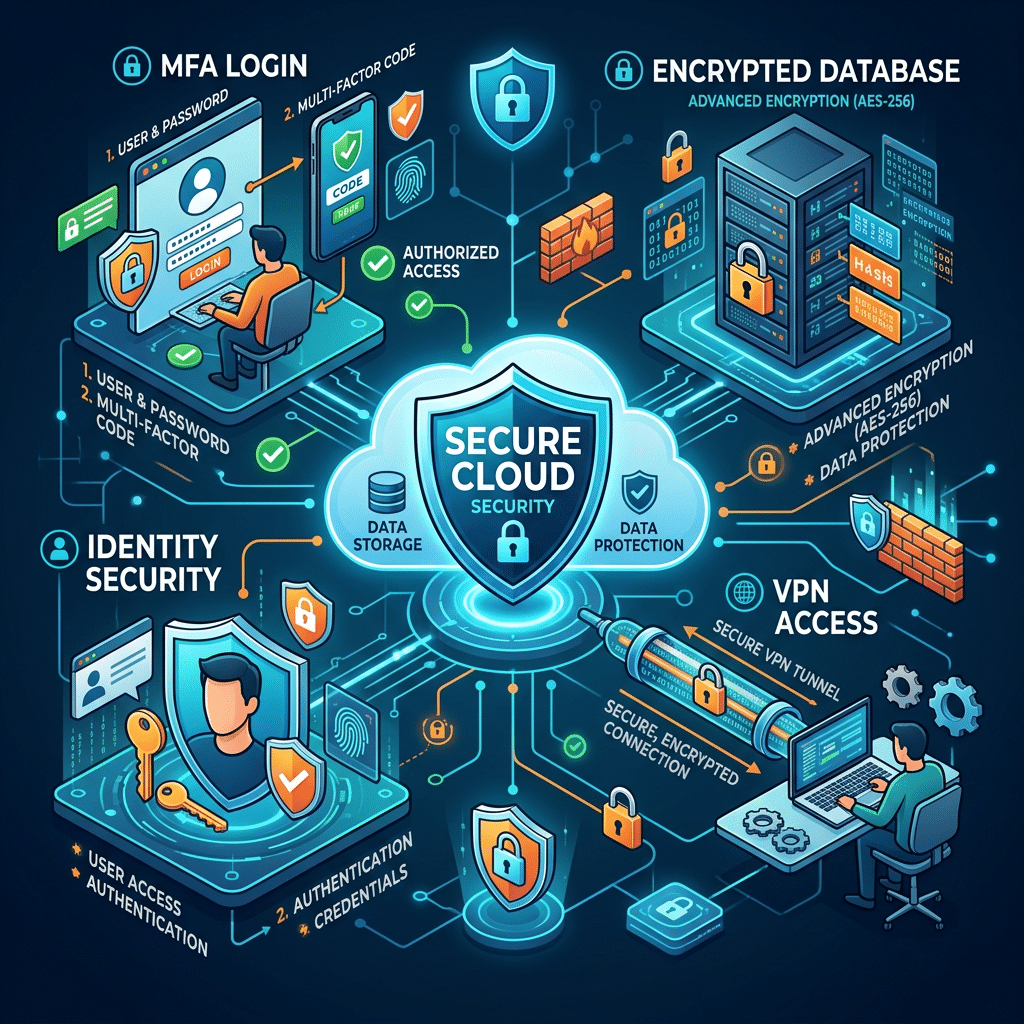
Healthcare organizations preparing for the HIPAA Security Rule Changes 2026 are expected to strengthen encryption coverage across databases, APIs, storage environments, communication channels, and backup systems. Partial encryption strategies are becoming increasingly difficult to justify in environments that handle sensitive patient data.
Identity security is also becoming central to compliance readiness. MFA is rapidly becoming the expected standard across EHR systems, VPN access, cloud platforms, administrative systems, and remote support environments. Organizations that still rely heavily on password-only authentication models are facing significantly higher operational and compliance risk under the HIPAA Security Rule Changes 2026.
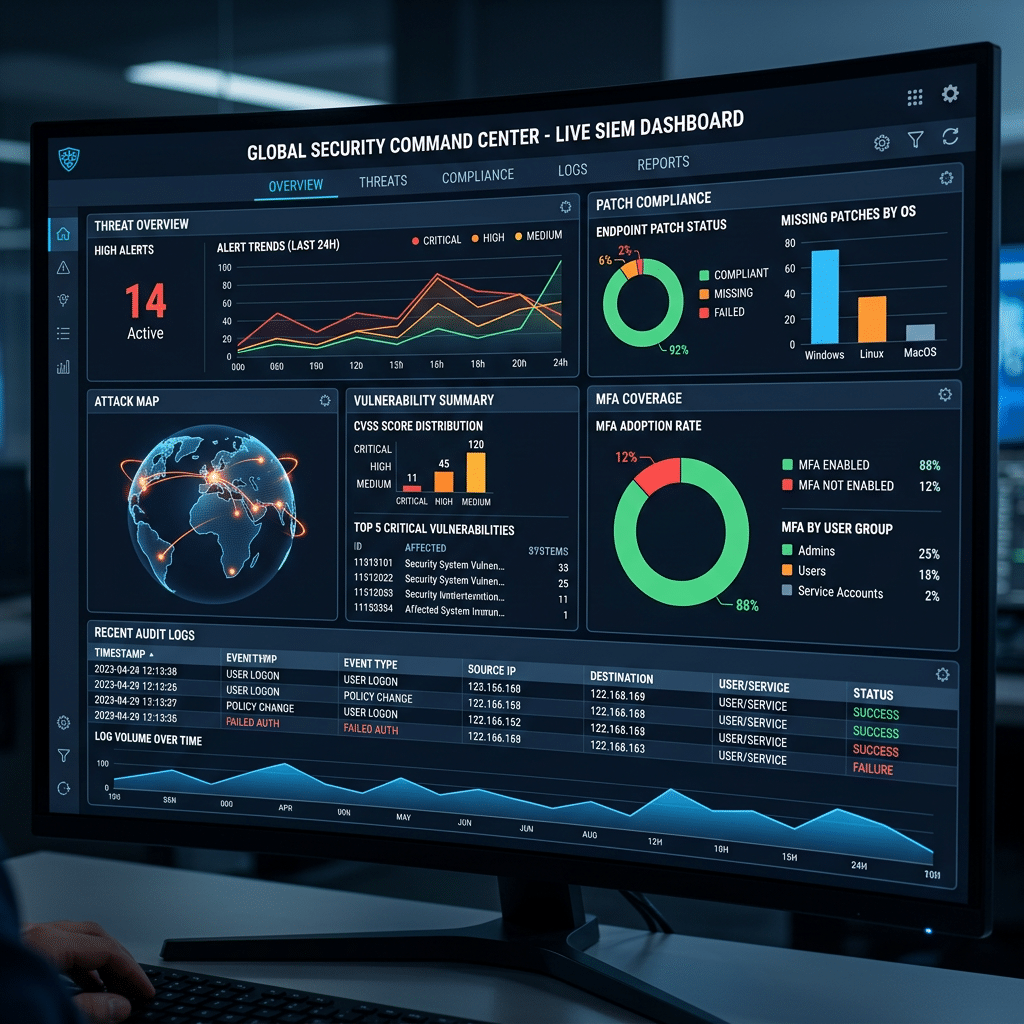
At the same time, annual compliance reviews are no longer enough. Continuous validation is becoming a core expectation. Vulnerability scanning, penetration testing, centralized logging, SIEM visibility, and documented recovery testing are steadily becoming operational requirements instead of optional security improvements.
The message across the healthcare sector is becoming increasingly clear: security programs must become operationally mature, continuously monitored, and defensible under scrutiny as organizations align with the HIPAA Security Rule Changes 2026.
This is where modernization partners play an increasingly important role. Vedhas combines cloud consulting, enterprise modernization, infrastructure transformation, DevOps practices, and compliance-aware delivery processes to help organizations modernize security capabilities without destabilizing existing healthcare operations.
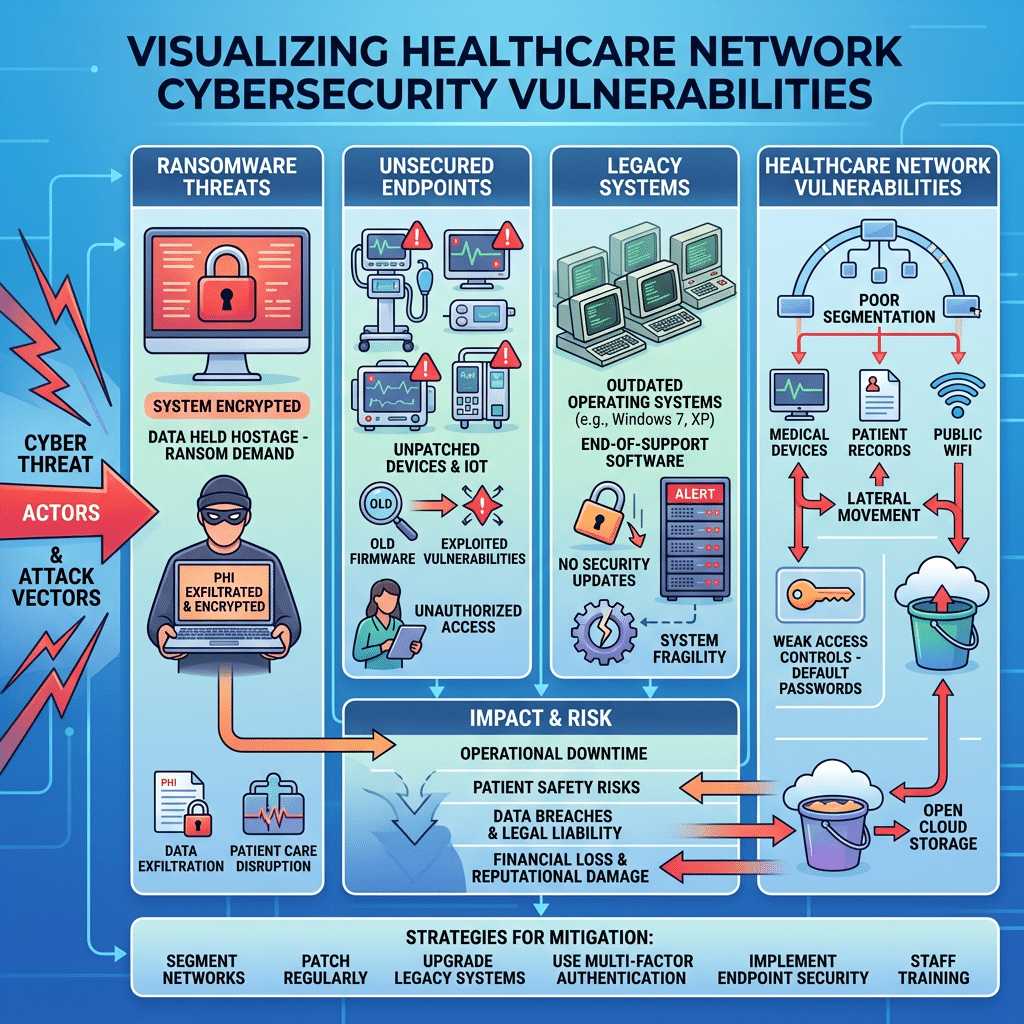
The Growing Risk Landscape in Healthcare
The urgency surrounding the HIPAA Security Rule Changes 2026 is closely tied to the growing scale of cyberattacks targeting healthcare organizations. Hospitals remain highly attractive targets because they rely on uninterrupted operations, manage enormous volumes of sensitive patient data, and often operate complex legacy environments that are difficult to secure consistently.
Many organizations continue to struggle with outdated systems, fragmented visibility, incomplete audit logging, unsupported operating systems, weak remote access controls, and delayed patch management practices. Under the HIPAA Security Rule Changes 2026, these weaknesses are no longer viewed as isolated technical problems. They increasingly become indicators of broader operational risk and insufficient safeguards.
The consequences extend far beyond regulatory penalties. Major breaches frequently result in operational downtime, clinical disruption, legal exposure, recovery expenses, insurance complications, and long-term reputation damage. In several cases, the loss of patient trust becomes far more damaging than the financial penalties themselves.
At the same time, maintaining outdated infrastructure increases operational costs year after year. Legacy systems often require more manual intervention while delivering weaker security protections and slower remediation capabilities. The result is an environment where compliance pressure, infrastructure debt, and cybersecurity risk reinforce one another.
Healthcare organizations are increasingly realizing that modernization is no longer simply a technology initiative. It has become a business resilience strategy.
The Cost of Delaying Modernization
Organizations that postpone modernization efforts often enter a cycle of increasing operational instability. Legacy systems rarely support modern security standards natively, forcing IT teams to rely on temporary fixes, fragmented tooling, inconsistent workflows, and manual intervention just to maintain basic operational continuity.
As the HIPAA Security Rule Changes 2026 continue raising expectations around measurable safeguards, these temporary workarounds become increasingly difficult to defend during audits, investigations, or cybersecurity incidents. Many healthcare organizations responding to the HIPAA Security Rule Changes 2026 are discovering that outdated infrastructure creates long-term operational and compliance exposure.
Older infrastructure frequently lacks capabilities such as modern authentication protocols, centralized logging integration, automated patching, granular access control, and native encryption support. This creates inconsistent security coverage across the environment while increasing operational complexity for internal teams.
Audit readiness also becomes significantly more difficult in fragmented environments. Organizations may need to demonstrate MFA enforcement, encryption coverage, vulnerability remediation timelines, recovery testing procedures, and incident response readiness with verifiable evidence. Without centralized governance and automation, generating this evidence becomes time-consuming and operationally expensive under the HIPAA Security Rule Changes 2026.
The operational burden grows steadily over time. Technical debt slows deployment cycles, increases downtime risk, lengthens remediation timelines, and creates greater dependence on legacy expertise that becomes harder to maintain year after year.
Vedhas works with organizations facing these exact challenges by helping modernize legacy infrastructure, streamline cloud adoption, standardize operational practices, and reduce long-term infrastructure complexity through phased modernization strategies rather than disruptive full-system replacements.
A Structured 90-Day Modernization Roadmap
The most effective response to the HIPAA Security Rule Changes 2026 is not a massive overnight transformation. It is a phased roadmap focused on practical improvements that reduce risk quickly while creating the foundation for deeper modernization over time.
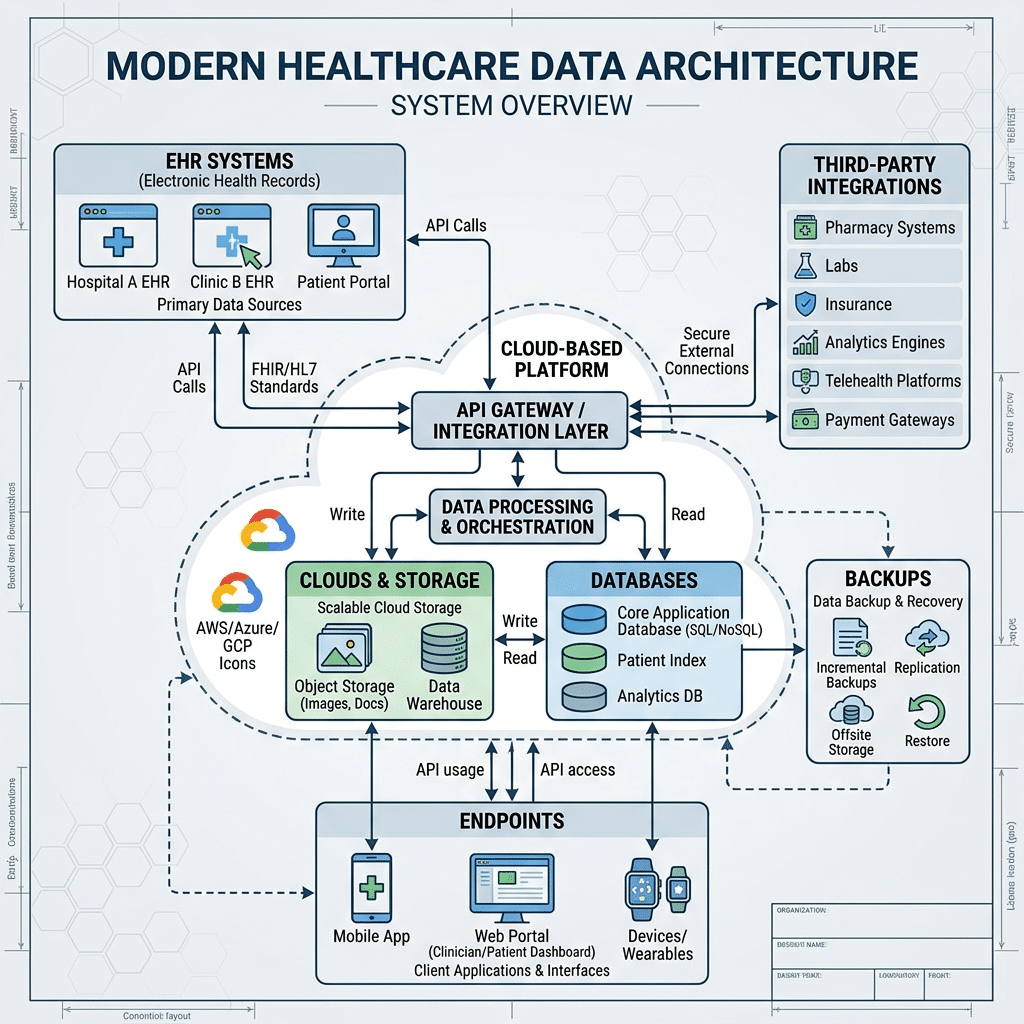
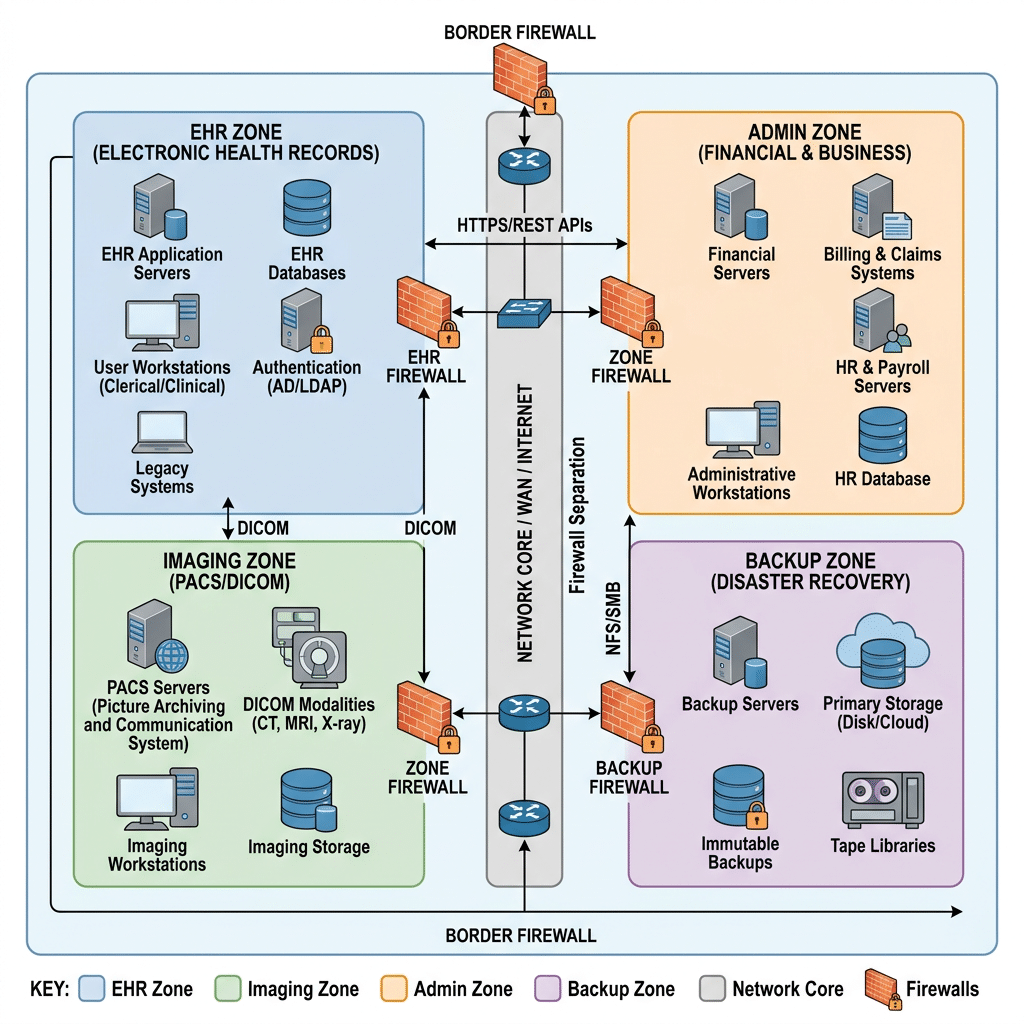
Most healthcare organizations operating under the HIPAA Security Rule Changes 2026 manage hybrid ecosystems that include on-premises systems, SaaS platforms, cloud infrastructure, third-party integrations, imaging systems, remote access environments, and legacy EHR applications. Because of this complexity, modernization efforts must balance security improvements with operational continuity.
The roadmap itself is built around four major modernization phases:
- Discovery and risk analysis
- Infrastructure hardening
- Advanced security controls and testing
- Governance and compliance readiness
Vedhas typically approaches modernization using phased implementation models that combine infrastructure assessments, modernization planning, application transformation, cloud readiness evaluation, and ongoing operational support. This helps healthcare organizations modernize incrementally while maintaining stability across mission-critical systems and aligning more effectively with the HIPAA Security Rule Changes 2026.
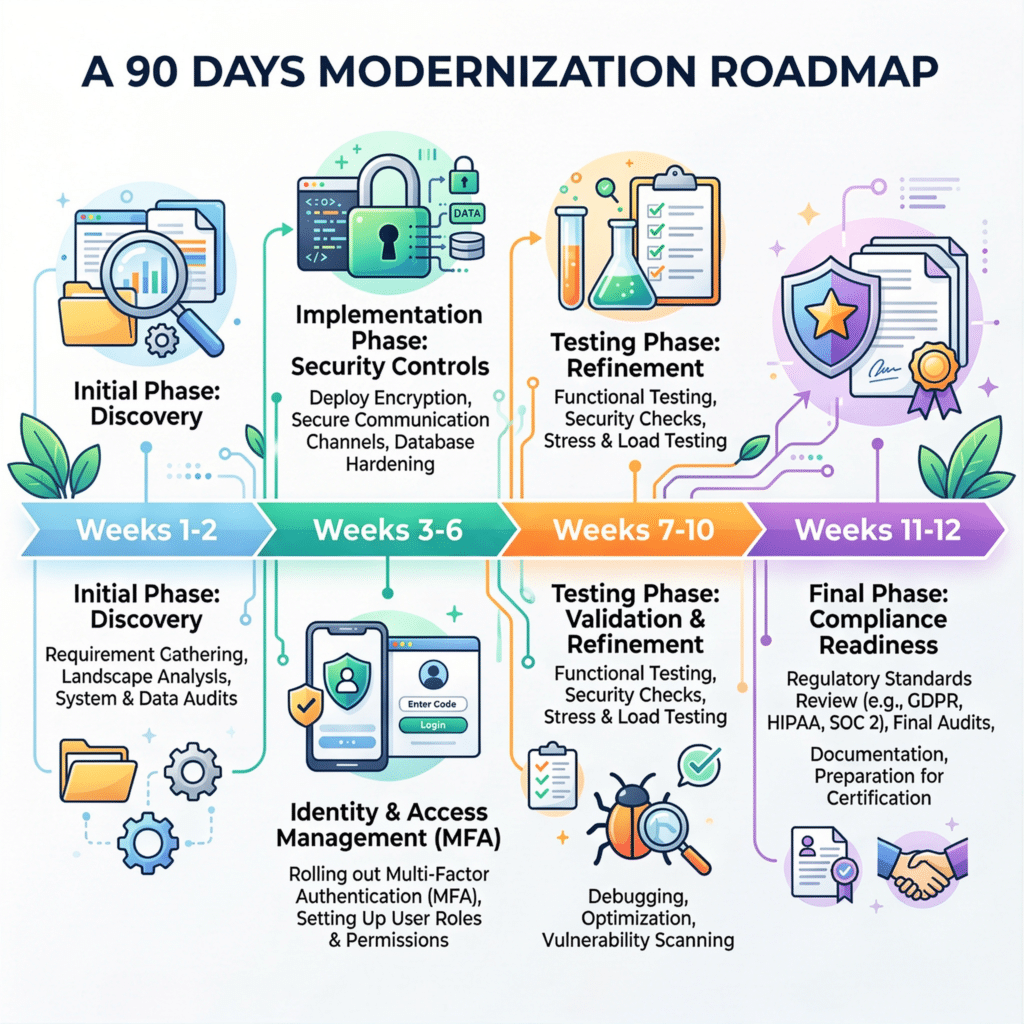
Weeks 1–2: Discovery and Gap Analysis
The first phase focuses entirely on visibility. Organizations cannot secure systems they do not fully understand.
During the first two weeks, healthcare IT teams should map how ePHI moves throughout the organization, including EHR platforms, billing systems, imaging applications, APIs, file storage environments, backups, remote access systems, and third-party integrations.
A detailed infrastructure inventory should also be created across servers, databases, cloud workloads, containers, administrative systems, endpoints, and network segments. This visibility becomes the foundation for every modernization decision that follows.
At the same time, organizations should conduct an initial risk assessment aligned with the HIPAA Security Rule Changes 2026. The assessment should evaluate encryption coverage, MFA adoption, logging capabilities, network segmentation maturity, vulnerability management processes, backup resilience, and incident response readiness.
Governance structures should also be established during this phase. Cross-functional leadership teams involving compliance, IT, security, operations, and clinical stakeholders should define priorities, escalation paths, reporting structures, and modernization ownership.
Organizations working with Vedhas often begin with infrastructure readiness assessments, modernization workshops, and technical due diligence exercises that identify operational bottlenecks, compliance exposure, and modernization priorities before implementation begins.
By the end of week two, organizations should have:
- A complete visibility map
- A prioritized risk register
- Defined governance ownership
- Executive alignment on modernization priorities
Weeks 3–6: Quick Wins and Infrastructure Hardening
The next phase focuses on high-impact improvements that reduce immediate risk exposure.
Healthcare organizations responding to the HIPAA Security Rule Changes 2026 should prioritize expanding encryption coverage across the environment. This often includes enabling Transparent Data Encryption (TDE), encrypting storage accounts and backups, enforcing TLS 1.2+ across APIs and applications, and securing endpoint devices and cloud storage environments.
MFA deployment should also accelerate rapidly during this phase, particularly across EHR systems, VPN access, remote administration tools, cloud platforms, virtualization systems, and identity management infrastructure.
At the same time, centralized logging should become operational. Security logs from infrastructure, networking systems, applications, and identity providers should feed into centralized monitoring or SIEM environments that support threat detection, incident investigation, audit reporting, and compliance evidence generation.
Infrastructure hardening efforts should also begin immediately. In many organizations, major risk reduction can be achieved through configuration modernization rather than complete system replacement. This includes disabling outdated protocols, removing unnecessary services, closing unused ports, standardizing baseline configurations, and eliminating unsupported software.
Vedhas frequently supports these initiatives through cloud infrastructure modernization, infrastructure automation, DevOps implementation, and secure application transformation strategies designed to improve scalability while strengthening operational resilience.
Weeks 7–10: Advanced Controls and Security Testing
Once foundational controls are in place, organizations should focus on deeper security architecture improvements.
Network segmentation becomes especially important under the HIPAA Security Rule Changes 2026 because it limits lateral movement during cyber incidents. Healthcare organizations should isolate EHR systems, analytics platforms, imaging environments, administrative infrastructure, backup systems, and identity services wherever possible.
Segmentation strategies may involve VLANs, firewall policies, virtual networks, identity-aware access controls, and zero-trust principles. Access between systems should follow least-privilege models with continuous monitoring and centralized logging enabled.
This phase should also formalize security testing processes. Many healthcare organizations also align internal security validation processes with the NIST Cybersecurity Framework to improve operational consistency and risk visibility. Vulnerability scanning, penetration testing schedules, remediation SLAs, configuration reviews, and patch management workflows should become standardized operational practices rather than occasional audit activities.
The objective is not simply deploying controls. Organizations must also validate that those controls operate consistently over time.
Healthcare organizations often struggle at this stage because many legacy systems were never designed for continuous validation or centralized monitoring. Vedhas helps address this challenge by introducing automation, governance frameworks, DevOps modernization practices, and scalable operational models that improve long-term maintainability while reducing infrastructure complexity.
Weeks 11–12: Documentation and Compliance Readiness
The final phase focuses on governance, documentation, and audit preparedness.
The HIPAA Security Rule Changes 2026 place increasing emphasis on proving that safeguards are implemented consistently and maintained operationally. Organizations should update or formalize policies covering encryption standards, MFA enforcement, logging and monitoring, vulnerability management, incident response, vendor oversight, and backup recovery procedures.
Internal compliance reviews should validate technical implementation evidence, policy alignment, remediation tracking, testing documentation, logging coverage, and assigned ownership responsibilities.
Incident response plans should also be modernized during this phase. Organizations should develop documented response playbooks covering ransomware attacks, credential compromise, infrastructure outages, insider threats, and data exfiltration scenarios. Recovery objectives should be tested wherever possible to validate operational resilience under realistic conditions.
By the end of the 90-day roadmap, healthcare organizations should possess a significantly stronger security baseline aligned with the operational expectations of the HIPAA Security Rule Changes 2026.
Vedhas supports organizations during this stage through governance alignment, reporting structures, post-deployment reviews, and ongoing operational support models that help teams sustain modernization momentum well beyond initial implementation.
Accelerating Secure Healthcare Applications with Native AOT .NET
Modernization is not only about compliance controls. Performance and operational efficiency also matter.
Healthcare organizations modernizing applications under the HIPAA Security Rule Changes 2026 can benefit from Native AOT deployments within .NET environments. Native AOT helps reduce application startup times, memory consumption, infrastructure overhead, and container image sizes, improving scalability while supporting faster deployment cycles.
A sample .NET configuration may include:
<Project Sdk="Microsoft.NET.Sdk.Web">
<PropertyGroup>
<TargetFramework>net8.0</TargetFramework>
<PublishAot>true</PublishAot>
<PublishTrimmed>true</PublishTrimmed>
<SelfContained>true</SelfContained>
<InvariantGlobalization>true</InvariantGlobalization>
<IsAotCompatible>true</IsAotCompatible>
<OptimizationPreference>Size</OptimizationPreference>
</PropertyGroup>
</Project>For organizations deploying frequent security updates, smaller deployment artifacts and faster startup times can improve patching efficiency while reducing deployment friction.
Automating Security Controls with Terraform
Automation is becoming increasingly important for maintaining long-term compliance consistency.
Organizations responding to the HIPAA Security Rule Changes 2026 should consider infrastructure-as-code practices using tools such as Terraform. Automated environments help reduce configuration drift, standardize deployments, simplify audits, accelerate remediation, and enforce security baselines more consistently. Organizations running healthcare workloads on Azure should also follow Microsoft’s recommended cloud security and encryption best practices.
A simplified Azure storage configuration example may look like:
resource "azurerm_storage_account" "secure" {
name = "prodsecuredata"
resource_group_name = azurerm_resource_group.prod.name
location = azurerm_resource_group.prod.location
account_tier = "Standard"
account_replication_type = "LRS"
https_traffic_only_enabled = true
blob_properties {
versioning_enabled = true
}
infrastructure_encryption_enabled = true
tags = {
environment = "production"
}
}
Vedhas incorporates automation, cloud governance, infrastructure modernization, and DevOps transformation practices into enterprise modernization initiatives to help organizations maintain operational consistency as compliance expectations continue evolving.
Legacy vs Modern HIPAA Compliance Environments
| Requirement | Legacy Environment | Modernized Environment |
| Encryption | Partial or inconsistent | Organization-wide encryption |
| Authentication | Password-only access | MFA and conditional access |
| Logging | Limited visibility | Centralized monitoring and SIEM |
| Patch Management | Manual updates | Automated remediation workflows |
| Network Security | Flat infrastructure | Segmented architectures |
| Testing | Annual assessments | Continuous validation |
| Recovery | Slow restoration | Defined RTO/RPO objectives |
| Vendor Oversight | Basic contracts | Structured security reviews |
Modernization is no longer simply a technology initiative. It is becoming a long-term operational resilience strategy.
Strategic Modernization Beyond the First 90 Days
The first 90 days establish momentum, but long-term modernization continues well beyond the initial roadmap.
Once foundational security improvements are complete, organizations can begin focusing on broader transformation initiatives such as legacy application modernization, cloud migration strategies, zero-trust expansion, DevSecOps integration, identity governance automation, advanced threat detection, and data lifecycle governance.
The organizations that respond most effectively to the HIPAA Security Rule Changes 2026 will treat modernization as an ongoing operational capability rather than a one-time compliance project.
This is where long-term modernization partnerships become increasingly valuable. Vedhas combines business consulting, cloud transformation expertise, application modernization, operational support, and enterprise technology strategy to help healthcare organizations continue evolving beyond their initial compliance milestones.
Building Trust Through Measurable Security
Modern healthcare security programs must demonstrate measurable progress.
Leadership teams increasingly expect visibility into encryption adoption, MFA coverage, patch compliance, vulnerability remediation timelines, incident response maturity, and recovery readiness. Dashboards, centralized reporting, and operational metrics help organizations track modernization progress while generating evidence for auditors, insurers, executive stakeholders, and business associates.
The healthcare organizations that modernize successfully are not simply improving compliance posture. They are improving operational resilience, reducing infrastructure risk, and strengthening patient trust.
At Vedhas, modernization initiatives are approached with a strong emphasis on measurable outcomes, transparent execution, and long-term operational stability — particularly for healthcare environments where uptime, security, and compliance directly impact patient confidence and business continuity.
The HIPAA Security Rule Changes 2026 are reshaping healthcare cybersecurity expectations. Organizations that modernize early will be better positioned to strengthen patient data protection, improve operational resilience, and respond confidently to evolving regulatory scrutiny.